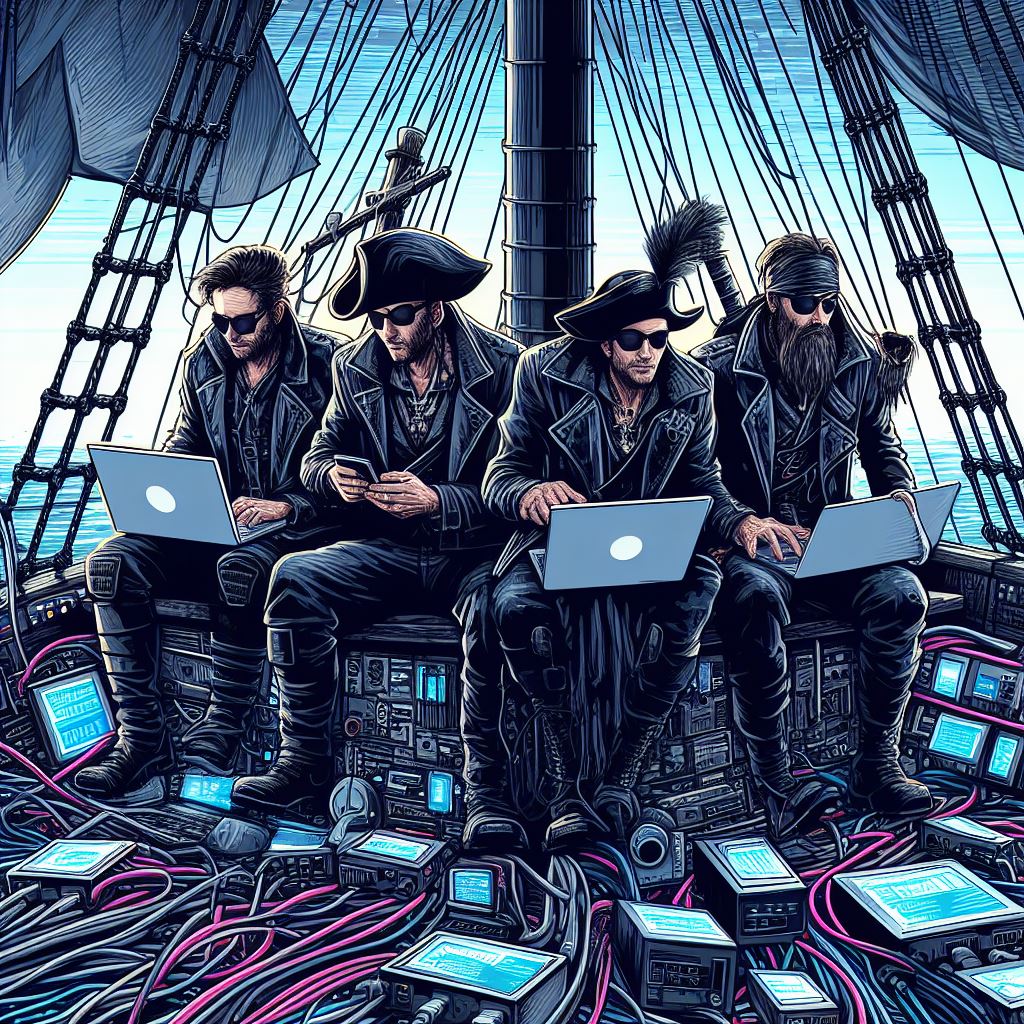
If you steer the ship of a modern organization, you face harsh truths that lurk just beneath the waves – cybersecurity threats multiply exponentially as data pirates deploy increasingly sophisticated techniques to breach defenses and capture riches. These bad actors’ cybercrime activities cost companies throughout the world trillions every year in damages with cost projected to exceed 10 trillion in the next couple of years (Cybercrime To Cost The World $9.5 trillion USD annually in 2024 (cybersecurityventures.com).
Many vessels still lack adequate defenses, relying on outdated maps, unarmored hulls, spare sails, and incompletely trained crews. Despite looming storms, many vessels still lack adequate protection. This leaves them exposed, caught between the shoals of compliance codes meant to protect their precious cargo, and the ghost ships trying to steal it.
This cybersecurity guide provides timely charts with vital safeguards for navigating the dangerous conditions ahead. Follow our recommendations to batten hatches, prepare crew, leverage experienced helmsmen, and more easily obtain the visas of cybersecurity insurance so that you can confidently chart full speed ahead.
Crewing Up to Combat Ever-Growing Threats
With threat sophistication typically cresting ahead of defenses, understanding evolving pirating tactics is critical to effectively repelling and even avoiding their assaults. Some common cyber threats include:
- Ransomware – Encrypts data into useless code until significant tribute is paid, holding systems hostage. Even after paying up, restoration takes weeks and data can still walk the plank or be sold into the black market to the highest bidders.
- Spear Phishing – Manipulates staff into surrendering credentials using psychological tricks. Mateys then stealthily infiltrate your decks seeking booty.
- Supply Chain Attacks– Strikes through trusted partners, piercing your hull while still in port. A secret underwater hatch is created for offloading cargo at any time.
- Distributed Denial-of-Service (DDoS) Attack– Bombards infrastructure blocking entrance to customers and commerce when uptime matters most—crippling ship-to-ship and ship-to-shore communications. The ripples can sink profit and reputation.
Highly organized hacker fleets now assail organizations worldwide, armed not with sword and cannon, but other attacks such MitM, password attacks, SQL injection attacks, Malware attacks, Zero-day exploits, and third-party breaches. These digital pirates relentlessly pursue paydays built on extortion, chaos, and stolen data. Their fleet contains vessels of all sizes and capabilities, looking for any vulnerability, large or small. They only need to find one hole to successfully attack your ship, whereas you must protect against every kind of attack boat, even those that haven’t been built yet, every time.
Lacking robust protection makes you an easy mark in the crosshairs. The size and frequency of assaults now outpaces even the Royal Navy. Those sailing underprepared make themselves easier targets. Protect what you value most before it falls into unscrupulous hands.
Navigating Ambiguous Waters Using Proven Guidance
Traversing ever-changing seas, ambiguous threats, and convoluted regulations requires drawing on generations of wisdom codified in frameworks like NIST CSF. It provides waypoints on operations all captains should adopt based on the potential hazards on the waters.
Attempting to single-handedly assess risks, install controls, monitor systems, and respond to incidents will quickly overwhelm inexperienced crews. Partnering with veteran navigators provides:
- Hand-drawn charts guiding you through compliance obligations
- Assistance outfitting your ship with defenses proven against modern pirates
- Around-the-clock patrols inspecting vulnerabilities and watching for threats
- Emergency “Coastguard” response when breached or held hostage
Take aboard knowledgeable IT managed service provider pilots so your crew can focus on smooth sailing ahead rather than constantly manning the bilge pumps. They bring enterprise-grade tools and expertise far exceeding the capabilities of landlubber businesses.
Using the CIA Triad for Protecting Your Most Vital Assets
A robust cybersecurity strategy safeguards your critical data using the CIA Triad: CONFIDENTIALITY, INTEGRITY, and ACCESSIBILITY. This requires:
- CONFIDENTIAL information secured through restricting access to authorized crew only and encrypting data.
- INTEGRITY of records ensured by maintaining accuracy and completeness to avoid disruption.
- ACCESSIBILITY of systems protected to prevent outages blocking trade and productivity.
A moment of folly like clicking a lure can bypass all defenses. A momentary lapse in discipline, like clicking a clever phishing email, can override even the strongest technical defenses.
This requires battening hatches, keeping the deck swabbed to prevent breach-enabling clutter, preparing contingency plans, and instilling SECURITY VIGILANCE in all crew through training. Without discipline even the best technical protections fail. Staying power requires culture, a consistent cybersecurity training schedule, and conduct, not just technology.
Adhering to Maritime Codes is Mandatory
Regulations like HIPAA, PCI and GDPR require privacy protections and breach vigilance proportionate to your data types, or face consequences – heavy fines, lawsuits, and even being scuttled.
- HIPAA – Up to $50,000 per improperly accessed record. A large breach could draw millions in penalties.
- PCI – Substantial fines and blacklisted from merchant voyages for exposing financial treasure.
- GDPR – Fines up to 4% of total bounty. Could sink even the heartiest privateers overnight.
You must implement controls from your industry’s compliance standards which correspond to your precious cargo. Lacking preparation makes you an easy target for regulators. Non-compliance courts catastrophe.
Cybersecurity Insurance to Protect Yourself Against Raising Storms
When sailing hazardous waters filled with icebergs and thieves, cybersecurity insurance provides protection should disaster strike. Cyber policies can cover costs like:
- Legal defenses and forensic investigations
- Notifying and providing credit monitoring for affected customers
- Negotiating with ransomware gangs
- Rebuilding reputation and trust after an incident
But qualifying for protection requires implementing security fundamentals – staff training, access controls, patching, etc. Non-adherence jeopardizes your ability to file claims and could result in regulatory fines for noncompliance.
Smooth Sailing Awaits with the Right Precautions or Set Sail Toward Peace of Mind
The cybersecurity seas will only become more unpredictable in the years ahead. By partnering with practiced navigators and implementing preparations outlined in this guide, you can traverse turbulent waters and complete voyages intact.
We can help crew your company with resilience mandatory to thrive in raging cyber waves. Don’t drift toward ruin by ignoring threats amassing over the horizon.
We will assess risks, modernize defenses, and provide ongoing guidance so you can sail ahead with confidence. Let us help crew your company with the cyber resilience mandatory to thrive on the open seas. The waters only grow rougher so let us voyage forward together. Contact us today to chart a heading built to withstand storms and pirates.